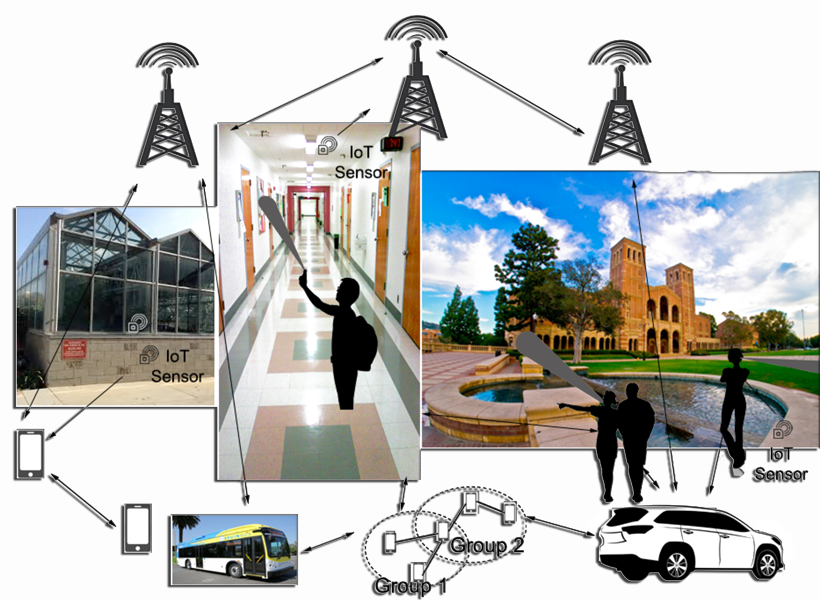
Technological advances have moved society into an exciting era of mobile computing. Our daily lives can be further enriched by a new generation of mobile applications, such as augmented reality (AR) which broadens one’s real-world perception by harmonizing sound, image, video, and sensors from multiple sources to aid comprehension and navigation. However, today’s Internet operates with the address-based TCP/IP protocol architecture developed 40 years ago, which greatly limits the full promises of these new applications. Thus, current AR implementations face challenges in performance, scalability and availability upon disasters. This proposed research project (ICE-AR) aims to develop a new wireless network architecture to address these limitations and provide pervasive support for these emerging applications.
The ICE-AR project team will apply and extend seven years of research efforts on Named Data Networking (NDN), a realization of the Information Centric Networking (ICN) vision, to create this new architecture. The design will emphasize application-level data naming, data-centric security and computing, asynchronous publishing and consumption, and efficient use of local and proximate resources. The architecture will unify latest advances in wireless communication with domain-specific computing technologies to accelerate AR at the wireless edge and deliver robust performance, with or without the pre-deployed infrastructure support.
Our Objectives
E Enable ICN in an operational demonstration system that integrates low-level wireless performance improvements with domain-specific acceleration as a service — explore the design and usage of computation at wireless edge.
D Develop the design of robust and resilient networking for an information system that comprehensively utilizes infrastructure resources as well as withstands massive infrastructure failures.
G Generate and generalize approaches that transition content delivery from monolithic, context-independent streams to highly granular, context-dependent approaches that can adapt rapidly and be delivered efficiently.
EExplore how to infuse comprehensive end-to-end security and identity privacy protection for users/applications–intrinsic security and privacy in all cyberspace elements at the edge, rather than an after-thought patch-on.